Your Vendors Are A Huge Asset, Unless They’re Mismanaged

Procuring equipment is a necessary part of managing any business, but this is often easier said than done. Your organization works with multiple vendors, which could be both confusing and time-consuming. How does your business manage its vendors, and is there a way to make this easier and more efficient?
Vendor Management Goes Both Ways
You might consider your vendors as assets, but the fact remains that they are also businesses just like yours. This means that, while you are trying to profit from your relationship with them, they are also trying to profit from their relationship with you. This doesn’t mean that this has to be the extent of your relationship with your vendors, but be sure to keep in mind that, ultimately, you are both for-profit institutions.
Vendor management isn’t about trying to earn discounts, cut costs, and outsmart the vendors into giving you a deal that’s heavy-handed in your favor. Rather, you want to form a trusting relationship with them so that both of your needs are served adequately. Approaching vendor management in this way can help you better understand the role that vendors play in the success of your organization. Forming this kind of relationship might seem challenging, but you’ll notice that you will receive higher quality of service, friendlier negotiations, and a closer working relationship.
How to Find the Right Vendor
Just like any relationship in the business world, there will be good fits that help your business flourish, while there will be bad fits that will cause more friction than progress. We’ll help you choose the right vendors for your business’s needs.
- Know what you want from your vendor. Once you’ve decided what role the vendor fulfills for your organization, you can then rank potential vendors in regard to how well they suit your needs.
- Create some documents that you can use to inform vendors of what your business requires:
- Request for Quote: This is helpful when pricing is the biggest pain point.
- Request for Information: Put together this document to see, at a glance, information regarding the market. If what you see is ideal, move on to the next document.
- Request for Proposals: This document allows the vendor to show how they can be beneficial to your organization. You present them with a problem that they then proceed to solve for you. If the document is too detailed or not detailed enough, you might get prospects that provide inaccurate quotes.
Negotiating with Vendors
Ultimately, you want a vendor who is willing to work with your organization to achieve mutual goals. Compromise is an important part of this process, as well as clear communications. After all, nobody wants to work with a vendor who is difficult to work with.
Ensure Ongoing Support As Needed
It’s usually the case that your relationship with a vendor won’t end after the purchase and implementation of a solution. You’ll generally form a service level agreement with your vendor of choice, which will determine how you receive service, how much is covered under your current contract, as well as what’s not covered. Unfortunately, in most cases, this means putting in a support ticket or holding for minutes on end while you’re waiting to get an issue resolved. You don’t have time to waste, so the ideal way to approach this dilemma is to have someone dedicated to dealing with vendors on your side. This way, you’ll always have access to someone who knows and understands your business’s SLAs and warranties, as well as someone who will make endless phone calls so that you don’t have to.
Catalyst Technology Group can be your go-to technology vendor management resource. To learn more about what we can do for your business, reach out to us at (317) 705-0333.
Tip of the Week: A URL Can Help Give Away A Phishing Attack

Back in 1995, scammers pulled the first phishing attack. They took the identity of AOL employees and requested the billing information of users through instant messaging. More sophisticated phishing attempts have evolved over the years, culminating in the commonly-seen email phishing attack, which tricks users into handing over personal or sensitive information. Phishing attacks can be seen through, so we’ll show you how you can identify threats before they become a problem.
How Phishing Emails Work
Above everything else, a phishing email needs to be convincing it if wants to trick anyone into opening it. For example, if you received an email from the bank filled to the brim with misspellings and blocked images, would you trust them? Phishing attempts have become more elaborate and more difficult to identify, as hackers understand that detail is important to trick users. Still, if you look closely, you’ll be able to identify a real message from a fake message designed to steal your information. In particular, you can check a URL for legitimacy.
The Tricks of Malicious URLs
Phishing attacks will typically require that the user clicks on a URL found in the phony email. They will then be redirected to a website that asks for their credentials. Most users who don’t know better will click on the link and not think twice about where it leads. Hackers understand this and try to distract them from caring by using strong language, urging them to take immediate action. This is how deceptive URLs try to succeed, but there is one fatal flaw in this tactic.
Avoiding Phishing Attempts
Phishing emails show all sorts of warning signs that you can identify if you’re observant. First, take note of any links that are in the message. Do NOT click them without first checking if they are legitimate. Hover over the link and see where it goes. Again, be extra careful to only hover over it and not click it. You should see where the URL goes, and if it’s not to the domain that it claims to be from, just avoid it. For example, if an email claims to be from paypal and wants you to click a link, the link should go to paypal.com–not payypal.com. Such an event could very well be a scam that wants to steal your username and password.
In other words, it’s a matter of common sense. Does the link look like it makes sense in the context of the sender?
If the answer is no, you’re probably staring at a phishing email. Don’t click the link, as it could perform any number of functions, from taking you to a malicious website or instigating a download of malicious files. Regardless, the end result will surely be detrimental to your organization and its network security.
Catalyst Technology Group can keep your network from suffering these types of breaches. To learn more about how we can keep phishing messages out of your inbox and monitor your network in real time for data breaches. To learn more, reach out to us at (317) 705-0333.
Keep Your Best Employee From Becoming Your Worst Problem With Data Management

Chances are that you, like most business owners, have assembled your staff very carefully, looking for people who are the best-in-class, willing to work their hardest for the good of the company. However, this staff will be made up of humans, and will therefore make mistakes. As such, you need to make sure that your data is managed in a way that keeps it safe.
Are you confident that you know where your company’s data is currently stored?
Unfortunately, if you are relying on your eager, diligent staff to allow you to answer “yes” to that question, then you may be answering incorrectly for the right reasons.
The thing about diligent employees is that, well, they’re diligent. They want to get the task at hand done to the best of their ability and as quickly as possible–and if that means they have to work from home, then that’s what they’re going to want to do. Which wouldn’t be a problem, if their home networks were nearly as secure as the ones you have in place at your business.
What’s to be done? You don’t want to discourage your more diligent employees, but you also want to make sure your data is safe.
The easy answer is to meet employees like these halfway. Give them access to a Virtual Private Network to help maximize their security as they access your data remotely. Ask them to have their personal devices checked by IT before they use them to access the network. Ask them if they’re willing to allow IT to remotely wipe their personal device if it should be lost or compromised as a precaution, if they were to be able to use it for work. An established Bring Your Own Device policy will make enforcing this requirement a little easier.
Of course, this does not mean that you should give all employees carte blanche access to all of your data. Network access control solutions are an effective way to restrict your employees from accessing data that is above their pay grade, either intentionally or by accident. Requiring authentication has become the norm in most of society, and so your loyal employees are unlikely to have a problem with it in the workplace. Passwords, PIN access, and other identification factors will prove useful in keeping employees where they are supposed to be, and able to access what they need for their job requirements.
The reason that it is so important to allow your employees to work as they wish is because it will allow them to be productive, without resorting to their own methods outside of company control, which are far less secure than what you have implemented.
For help implementing these features into your IT infrastructure, make sure you give Catalyst Technology Group a call. We have the solutions you need to safely allow your enthusiastic employees to work the way they work best. Give us a call at (317) 705-0333 today.
7 Habits of Highly Effective PC Users
Security is an incredibly important part of running any business, but unless you’re a professional IT technician, you may run into a couple of roadblocks while implementing a solution. Chief among these is not knowing exactly what you’re protecting your business from. Keep the following tips in mind to reinforce your security strategy and preserve your business infrastructure’s integrity.
Implement Strong Passwords
Weak passwords are, not surprisingly, a major problem for all types of businesses. Strong passwords are practically impossible to remember, so users tend to opt for easy, less secure passwords when it comes time to create a new one. The truth of the matter is that strong passwords are essential if you want to optimize security. Be sure to include both upper and lower-case letters, numbers, and special symbols in your credentials.
Use a Password Manager
The increase in popularity for password managers means that there is no longer any reason not to use secure passwords. Since the main reason not to use a secure password is that they are difficult to remember, the password manager handles this task for you. Passwords are stored in a secure digital space where they are called upon as needed, allowing you to optimize security like never before.
Implement Two-Factor Authentication
Passwords might not be the most secure method of protecting accounts, but a method called two-factor authentication can help. Two-factor authentication creates secondary credentials that you use to access an account. These credentials are usually delivered via a secondary email account or a personal device. If hackers see that they need other credentials besides your username or password, they might think twice about attempting to breach your account. After all, hackers like simplicity, and if they have to work extra hard for something, they might be less likely to pursue the attempt.
Prevent Unnecessary Online Payments
The Internet has allowed organizations and individuals to shift the bulk of their consumer behaviors to online retailers. While it might be tempting to just use your credit cards for any online purchase, it’s important to remember that not every website will be protected for such transactions. You should only use credentials on encrypted websites so that they cannot be stolen by onlooking hackers. Always be sure to check the security protocol used by a website before entering any sensitive information into them.
Avoid Links and Attachments from Unknown Messages
You might receive spam messages in your email inbox, and it’s likely that they will contain links and attachments laden with malware or viruses. If they don’t directly contain malware, they might lead to malicious websites where your credentials are stolen. In fact, one of the most dangerous threats out there–ransomware–is typically distributed via phishing attacks within an email. To dodge these threats, you should implement an enterprise-level spam prevention solution.
Stay Away from Public Wi-Fi
Cyber criminals will use public Wi-Fi connections for the express reason that people tend to go where there is a free connection to use. Some examples are coffee shops, local libraries, or public areas where business owners gather. The reason for this is that many public Wi-Fi connections are unsecured, so hackers will have a field day compared to when they are trying to crack a secured, private Wi-Fi connection.
Upgrade Your Operating Systems
Older operating systems aren’t as secure as their newer ones. Nowhere is this more dangerous for a business than when they still run unsupported operating systems like Windows XP. New software offers almost continuous testing, so as critical security flaws are found they are patched, ensuring users have a secure and reliable user experience.
Your business’s security should be at the top of your mind. However, you might not have time to worry about it, so why not reach out to us at Catalyst Technology Group? Our trusted professionals can help you keep your organization’s network secure. To learn more, reach out to us at (317) 705-0333.
It’s Time to Write a Eulogy for the Internet as We Know It

The Internet is prone to change. We all know this and have experienced it firsthand. Even though we may understand this reality, it can still be rather shocking when we’re confronted with it. The latest statistics show us how the current changes of the Internet have huge implications about how we’ll all interact with the web moving forward, which may spell doom for doing “online business as usual.”
A recent report by Forrester reveals that we are spending 85 percent of our time on our mobile phones using apps, and only 15 percent in the browser. Pair this with another major trend that saw a tipping point in 2014 when more people began accessing the Internet through mobile apps than desktop computers, and you really begin to see clearly just how the web is truly changing.
By changing, we mean that people are spending far less time on their desktops (and dramatically more so on their mobile devices) perusing the Internet by going from website to website, and far more of their time online using mobile apps. Does this mean you, as a business owner, should therefore shift all of your online efforts to mobile apps?
Not necessarily, seeing as another finding from Forrester’s study shows that people are spending 85 percent of their time on their mobile device utilizing only five apps, which includes obvious apps such as Facebook and Google.
As net neutrality continues to be threatened by legislation influenced by special interests, the trend shown by these statistics threaten the same freedoms we enjoy online, only from a different angle. That angle: the business interests of a handful of companies that own these popular mobile platforms will end up dominating and controlling the online conversation. Business2Community describes it like this: “This reality on the commercial web is now being revealed as we are witnessing the rise of a duopoly. Google and Facebook. Today 90 percent of all advertising growth on digital is coming from these two companies.”
Now, don’t get us wrong, as long as there’s an Internet you’ll still be able to publish your message (whether it be personal or professional) in the same ways that were popular 10 years ago before the iPhone hit the scene (like using websites, forums, email, etc.). It’s just that, good luck getting anybody to actually listen to your message without the help of Facebook and Google to drive traffic to your site. Furthermore, online content that’s not tailored for mobile will continue to lose influence as the Internet continues to evolve in the ways that it is.
While the vast majority of us are powerless to stop such changes, all those who value the open Web have every right to mourn what the web’s becomining. An appropriate eulogy can be found in the words of Tim Berners-Lee’s (the inventor of the World Wide Web) 1995 utopian vision of how the Internet can change the world for good. Berners-Lee described his vision of the web as “an open platform that would allow everyone, everywhere to share information, access opportunities, and collaborate across geographic and cultural boundaries.”
While the web is more accessible and “open” today than ever before, one must put an asterisk at the end of this 1995 statement that communicates, “at the terms of Google and Facebook.”
From a business standpoint, the ongoing changes of the Internet presents a challenge that’s inherent with the use of any technology–the challenge to keep up with and anticipate trends, and to adapt your business model accordingly. Technology can change suddenly and you owe it to the continuity of your business to be in the know. Thankfully, you’ve got the technology experts at Catalyst Technology Group to navigate this changing world of technology for you.
Tip of the Week: How to Encrypt Files on Your Windows PC

Encryption is one of the most effective ways to secure a file, and even the average user can take full advantage of it on their Windows PC. In essence, you can arrange for your files to appear as random numbers, letters, and special characters in the event that an unauthorized user accesses them.You might be surprised to learn that even your Windows PC has encryption options so that you can protect your sensitive information if so desired.
Once you’ve encrypted a file, don’t think that it’s encrypted for good. You’ll have access to a decryption key, which is used to read the file again after the encryption process. Think of it as the picture on the box that lets you put a jigsaw puzzle back together after it’s been ripped apart and scattered on the floor.
Encryption has been all over the news lately, as ransomware attacks like WannaCry have become a blight for users everywhere. Hackers use ransomware to encrypt files against the user’s will, and they hold the decryption key hostage in an attempt to extort a ransom from the user. While the method of use is quite different for ransomware, it does show how good encryption can be for keeping unwanted users from accessing sensitive information.
NOTE: Before breaking down the steps to encrypting a file, we want to make it clear that data security and encryption is not for everyone to use without discrimination. The majority of users will want to entrust their data and its integrity to an IT Professional, like those at Catalyst Technology Group. IT Techs will determine which data should be encrypted, evaluate that it is done properly and ensure that the correct parties are able to access the data while keeping threats out. It’s extremely important that you don’t encrypt data in a shared environment. If you encrypt shared data, users that would normally have access to the data, won’t. In cases like this, it’s better to let a software solution implemented by IT do the heavy lifting for your company’s standardized file encryption.
To encrypt a file or folder in Windows, locate the data that you want to encrypt. Next, follow these steps.
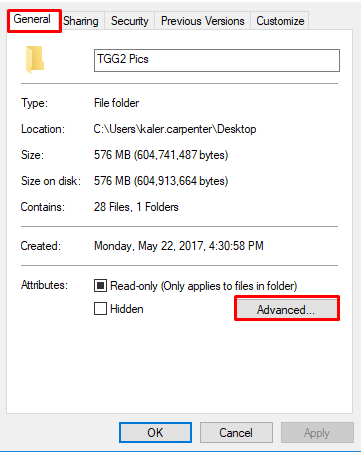
Select the file or folder, right-click it, and go to Properties.
Next, a new window will open. Select the General tab and click the Advanced button.
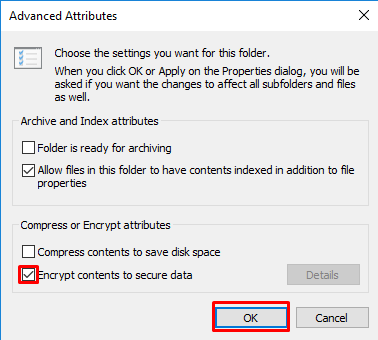
Check the box that says Encrypt contents to secure data. With this box selected, you should next click Apply and OK.
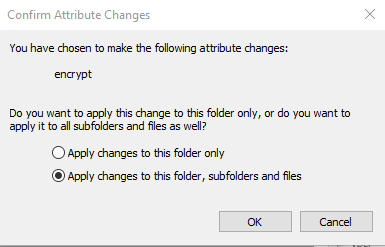
Depending on whether you want to encrypt a single file or a folder, you’ll see a new window that asks you to confirm just how much data you’ll be encrypting. Select the desired button and click OK.
Now your file should be encrypted, as indicated by the padlock on your file’s icon. It’s safe to say that your file is a bit more secure now, but encryption isn’t an absolute guarantee, and you shouldn’t rely on it completely. For business purposes, we recommend something a bit more comprehensive.
If you need even more help protecting your business’s assets, don’t hesitate to reach out to Catalyst Technology Group at (317) 705-0333.
When Juggling Business Responsibilities, You Can’t Afford to Drop IT Maintenance

The business world increasingly relies on IT services. Regardless of which industry you fall into, IT will undoubtedly play a major role in how your business functions on a daily basis. Businesses also need their technology to remain in proper working order, but this is easier said than done–especially if you don’t have the luxury of an in-house IT department. Thankfully, managed service providers make this much less difficult.
Compared to the traditional break-fix model of IT management, a managed IT provider aims to take a different, more proactive approach. Instead of managing your technology yourself and paying for maintenance when a system has failed, a MSP will take measures to keep your IT in proper working order so that it doesn’t leave you high and dry. Another imperative detail to include is that a managed IT provider takes care of your IT solutions so that you don’t have to, keeping you from spending time on business-disrupting IT troubles and preventing downtime as a whole.
For an example, consider the following scenario and how MSPs can influence how you do business.
It goes without saying that managing a business might have you spread a bit thin. Some tasks will naturally be sidelined in favor of more important initiatives. For example, installing updates for your various technology solutions is a task that might be pushed to the side, even though they are needed, simply because it’s a time-consuming process. Therefore, you miss out on critical opportunities and benefits that you could gain from updating your technology regularly.
Perhaps you are running a version of your operating system or program that is vulnerable to a serious threat. Without a proper update or patch, this vulnerability could lead to your business suffering from downtime or data breaches. It might not seem like there’s time in the day to patch up this vulnerability, but your organization can suffer from a delayed reaction to this vulnerability. Yet, juggling all of your responsibilities makes a timely approach to this issue, which has yet to show any real signs of even being an issue, just about impossible.
Managed services allow your organization to receive technology assistance from an MSP, including real-time monitoring and management, as well as updates as they are needed. This means that your applications will always remain up-to-date without your organization taking time out of its already-full schedule to make sure they happen. Since most maintenance can be performed remotely during the company’s off-hours, you can avoid in-house distractions and downtime.
Of course, this is only a singular example of how managed IT services can help your organization. If you want to know more about managed IT, reach out to Catalyst Technology Group at (317) 705-0333.
Take Advantage of Big Data to One-Up the Competition

Your business’s IT strategy is of incredible importance, especially when you consider how much your operations stand to benefit from a functional infrastructure. More than anything, though, IT can ensure that your business remains competitive in a world where the slightest advantage can mean all the difference.
With big data on the rise, let’s take a look at how it can help your business stand out amongst the crowd.
Big Data Changes the Rules
Big data is capable of affecting an industry on a large scale. Let’s say that one business starts to look at the way in which data trends affect the way that they approach their services and business model. They will start to see ways in which they can improve the way they do business. In turn, more and more businesses will look toward implementing big data, which makes it a new industry standard, completely changing the way that the industry operates.
Big Data Allows Businesses to Outperform Rivals
Being “in-the-know” is of the utmost importance in the business world, and the more data that you collect, the more information you have at your disposal. It’s as simple as this; big data allows businesses to gain a competitive advantage against their rivals. Being able to strategically look at statistics and analytics helps businesses to make better, more educated decisions about how to move forward.
Big Data Can Outright Create New Businesses
Big data has the opportunity to change business models so drastically that some organizations may split themselves up to create new business opportunities. Alternatively, businesses may create new departments within their organizations that focus on the analysis of this data. These departments can then deploy the data for a number of functions, including improving operations as a whole internally, or looking at external factors that could bring in more revenue, such as consumer behavior patterns.
Does your business leverage big data to its advantage? It could be just the thing you need to get a leg up on the competition. Catalyst Technology Group can consult you on how best to take advantage of data collection and delegation within your business and consumer base. To learn more, reach out to us at (317) 705-0333.
Tip of the Week: 11 Security Best Practices Every User Should Know

You might spend a significant amount of time thinking about your business’s security practices, but the same can’t be said for your organization’s employees. Unless you give them a reason to care about security, they likely won’t. The resulting apathy could eventually become serious problems that could hinder operations in the long run, or worse, expose your business to threats that could put your employees and your clients in danger.
In order to keep these instances to a minimum, consult the following cheat sheet. This will give your employees a great way to follow critical best practices.
Essential Cybersecurity Considerations
- Use the company’s network to store files: Always store your organization’s data on an in-house network. This is because any files stored locally on your desktop might not get backed up. Do not use personal cloud accounts, like Google Drive or Dropbox, to save or share company-owned documents.
- Never leave your workstation unlocked and unattended: Always lock your computer using the Windows Key + L shortcut before stepping away from it, even if only for a moment.
- Don’t connect unknown devices to your work PC: This is especially important for small devices like USB drives. You never know what could be on them.
- Don’t download or install applications without approval: If you download an app without permission from IT or a network administrator, you could cause problems for other employees. Always ask for permission before downloading or installing software.
- Don’t respond to unsolicited or suspicious emails: If you receive a message that has an unknown or unfamiliar sender, it could contain malicious ransomware or other nasty threats. Be sure to notify IT immediately so that they can investigate the issue. Be especially cautious around unsolicited proposals or resumes.
- Don’t accept support from unexpected callers: If you receive a phone call from someone claiming to be from Microsoft support (or other well-known companies), just hang up. These callers are often fraudsters hoping to remote into your PC and access company information.
- Adhere to password best practices: Keep your passwords strong and complex at all times, and never use the same password more than once.
- Get approval for mobile devices from your manager: Don’t use your smartphone, tablet, or laptop for work purposes until you’ve been granted approval. This is to keep company data as secure as possible.
- If you see someone, tell someone: If you think that something is out of the ordinary, like an intruder in the workplace, be sure to alert management. Visitors should not be allowed to roam around the office unattended.
- Think twice before clicking: If you’ve received a link in any correspondence, you should avoid clicking on it until you’re sure it’s from a trusted source. Links can often be considered cyber threats, especially those that are in spam messages.
- Report issues as soon as they appear: If you experience something that seems troublesome, report the issue to management immediately. Proactive vigilance is the best way to prevent downtime, and it only serves to make your job easier.
Print this list out and hand it off to any employees who could use training on security best practices.
Keeping the business secure isn’t just your responsibility–everyone should be involved in the process. By following this list of best practices, you stand to protect your business against threats that could harm operations. To learn more about how to secure your business, including external technology solutions that prevent issues from transforming into major problems, reach out to us at (317) 705-0333.
100+ Years Ago, IBM Started Just Like Any Other Business

Of the many technology companies in the public eye, IBM is one of the oldest and perhaps the most recognizable–but do you know the story behind Big Blue? It’s a history of innovation and revolution in computing that stretches back over 100 years, to when it was created by uniting three existing companies.
In 1911, a man named Charles Runlet Flint merged two of his existing companies, International Time Recording Company and Computing Scale Company of America with a critical third company that he had just acquired: Tabulating Machine Company. This new company was known as the Computing-Tabulating-Recording Company (or CTR).
The machines made by CTR were capable of sorting, analyzing, and eventually running calculations based on punch cards that were input into the machine. While this development had clear business applications in hindsight, it wasn’t until the controversial Thomas Watson was brought in as company president (after deftly avoiding lasting consequences from a conviction of violating the Sherman Antitrust Act–the act that bans monopolies) that the value of the tabulating division was focused upon.
Not only did Watson know his target audience well enough to know that the business-oriented tabulating machines would be in high demand as the United States became increasingly business-oriented itself, but he also understood the value of presenting CTR’s offerings as a service, rather than a product. This arrangement proved to be mutually successful for both CTR and its clients, as the sales team was able to inform the company of what their clients wanted to see from them next, thereby allowing the needs of their clients to be met.
By 1924, CTR had been renamed to International Business Machines to reflect the consolidation of the business and echo the timeless feel of other large brands of the day. 1925 saw Watson take up responsibilities as both the chief executive officer and the chief operating officer. In the following years, IBM would thrive in the face of the Great Depression, only receiving a boost from the federal bureaucracies’ need for computing devices after President Roosevelt’s New Deal mandates. Demand for the tabulation machines continued to increase during wartime, and by the time Thomas Watson, Jr. was brought on as his father’s successor in 1952, computers were slowly becoming more and more common in the office environment. Many companies had a simple transition, as they were simply trading their IBM tabulators for computers.
IBM truly went global in 1949, offering sales worldwide in a total of 58 countries. IBM World Trade Corporation dominated the global market everywhere but Japan and the United Kingdom, achieving a market share of (only) 33 percent in those countries.
However, in 1952, IBM was again hit by an antitrust lawsuit from the US government, and more critically, another from a niche computer pioneer called Control Data Corporation. IBM powered through these challenges, as well as shifts in leadership until the 1980s. At this point, Big Blue began to falter under pressure from other niche competitors. As a result, the company changed their management strategy, and weathered through business fluctuations until 2004, when they again stabilized their success rate.
IBM’s story of one of success, and there are lessons to be learned here for your own business. By forming the right partnerships and providing a product or service that’s in growing demand, your company can grow exponentially. IBM also shows business owners how to overcome challenges, like diversifying what you do in order to weather the inevitable changes in the marketplace, as well the importance of strong leadership. By learning from the successes of companies like IBM, who knows, maybe your SMB can do what it takes to rise to the top!

