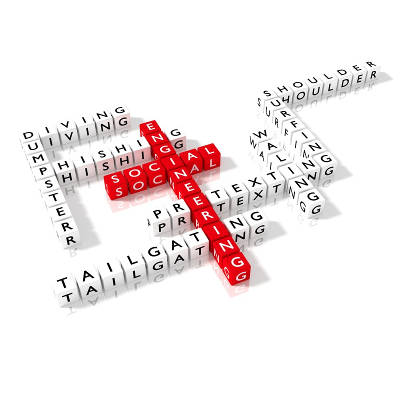
Could You Identify a Social Engineering Attack?
Social engineering can allow a cybercriminal to access networks without being hampered by the security solutions that a business has in place. Through the manipulation of the human element of a company, its critical resources are exposed. In order to protect your business against the threat of a social engineer, there has to be an overall awareness in your company culture.
Why Social Engineering Works
One of the main reasons that social engineering can be such an effective tactic for cybercriminals is because, rather than telling the target what they want to hear, the target is told what they expect to hear. By coming forward under the guise of someone who should be coming forward, the cybercriminal is able to extract information from unwitting staff members, adding to their intel through intensive online research.
These are the key factors that allow these kinds of attacks to be as successful as they are. The methods used by social engineers aren’t the kind that immediately come to mind when one thinks about cyberattacks. Since the attack doesn’t typically resemble more well-known threats like ransomware, these attacks are often able to infiltrate their target without any suspicion. Additionally, there is an excess of information available online, known as open-source intelligence, that provides the social engineer with the knowledge they need to craft their approach.
This open-source intelligence can come from a variety of places, making the social engineer’s job that much easier. There is plenty of information readily available on the Internet, all it takes is looking in the right place.
Sample Information
While it’s no secret that there is a ton of information online, the true scope of what is available can be alarming when all laid out. The following information can all be found if one knows where to look, and is by no means a comprehensive list of what is there:
Technological Details
Considering how valuable a cybercriminal would find the details of what technology is used in a business, these details are remarkably easy for cybercriminals to find. Companies will often show their hand in online job postings, identifying the hardware and software that they use in order to find someone with the experience. This not only ensures that qualified applicants send in their resumes, it also allows cybercriminals to send in the exploits needed to take the company down. Social media posts can also share this information–the wrong picture could give access to networking hardware and other critical and sensitive data.
Employee Data
On the topic of social media, sensitive company information can easily leak through oversharing. Employee activities that are shared or tweeted can provide a cybercriminal with crucial insights. Images can create an even bigger problem. If not scrutinized before posting, you can inadvertently display key details, from the data on the screens to the model of the computer that holds the data.
Furthermore, employees using social media carelessly can deliver more invaluable data for a cybercriminal to leverage. Discussing work schedules or even sharing specifics of work experience can potentially put your business at risk.
External Companies
Unfortunately, social engineering attacks can leverage data that you have minimal control over against your business as well, as other companies and vendors you do business with may share their experience with you as evidence of their value. Furthermore, if your janitorial services and trash pickup providers aren’t secure, your data could be stolen after it has left your property.
So while it is absolutely critical to leverage cyber protections for your data’s security, including solutions like firewalls and authentication measures, your employees also need to have their eyes peeled for the threat of social engineering. Every business needs to have a plan to avoid and mitigate the threat of social engineering. Catalyst Technology Group can help.
For more information, call (317) 705-0333.
Would Your Users Fall For These Social Engineering Schemes?

Social engineering is one of the trickiest parts of protecting your organization. It might sound like something out of a science fiction flick, but it’s one of the most dangerous attacks that a hacker can use against your business. Social engineering attempts to manipulate the target into giving away sensitive credentials or personal information for the purpose of stealing identities and other malicious intentions.
Here are some of the most popular social engineering hacks that you’ll have to watch out for in the business world.
- Vishing: More people are aware of phishing attacks than ever before, so naturally hackers had to pick up the slack somehow. Vishing is the alternative option that they are now trying to use, which features a voicemail asking for personal information.
- HTTPS: SSL certificates can make sure that users are aware of whether or not a website is secure enough to protect your personal information. However, HTTPS doesn’t necessarily mean that a website is using security. Hackers can lure in victims by providing “free” SSL certificates to organizations, providing them with a false sense of security. You need to find proof that the website using SSL has an extended validation (EV-SSL), which is not offered for free at all. You’ll see a green bar in the URL bar when this type of encryption is available.
- Website Copycats: Some scammers have even gone so far as to make websites that look exactly like reputable sites that are designed to harvest credentials or infect computers with malware. One example of this is the Equifax data loss incident which occurred in June 2017. Equifax had set up a website to help clients who had their information stolen, which used the URL equifaxsecurity2017.com. However, hackers capitalized on this event and created a spoof website using the domain securityequifax2017.com. The result tricked Equifax themselves. Here are some tips to help you avoid these spoofed websites:
- Make sure the URL is correct
- Don’t give information to sites that aren’t using EV-SSL
- Look for seals of trust from reputable IT security websites
- Be on the lookout for spelling errors, typos, or broken English
- Every Word Password Theft: Hacking tools have certainly developed into more sophisticated threats, going so far as to utilize every single word in the dictionary to crack passwords. These password crackers can create hundreds of thousands of credentials in a matter of minutes, all using a dictionary attack against unwary users. Therefore, the best approach to creating strong passwords is to use numbers, letters, and symbols to make a mixture that nobody would expect.
Online threats can be a considerable problem for your organization, especially when they use each and every exploit against you. Thankfully, with some proactive measures that can keep your business safe, you’ll have a much easier time going about your online duties without exposing your data to threats. To learn more about how to protect your business, reach out to us at (317) 705-0333.

