Looking at the Landscape of Email Fraud

Email is arguably the most popular method of business correspondence in existence. It’s fast, economical, securable, easy to store/archive, and searchable in a way that traditional, physical records can’t compete with. With billions of emails sent every day from all over the globe, there is a considerable amount of sensitive information transmitted within these communications. The criminal element is looking for every opportunity to steal and exploit personal data, as well as take advantage of vulnerabilities to gain access to a company’s data or network.
One particularly effective method of email fraud is impersonation. Sometimes falling under the categories of phishing, whaling, or SMiShing, impersonation email emulates a legitimate address from a non-threatening source that convinces the user to take an action. An example of an impersonating email fraud would be a user transferring funds to a 3rd party account on the order of what they believe is a legitimate message from their CEO, but actually originates from a spoofed email address. Another example would be if someone opened an email attachment that appeared to be a legitimate spreadsheet but actually introduces ransomware into their network.
Email Security by the Numbers
For those who are looking to visualize the risks associated with email fraud, here’s a look at a few recent statistics that show just how big of a problem it can be for a business.
- In 2017, the number of worldwide email users will top 3.7 billion, or about half of the worldwide population uses email in 2017.
- Phishing attacks make up about 91% of all attempted cyberattacks.
- Top three reasons people are duped by phishing emails are curiosity (13.7%), fear (13.4%), and urgency (13.2%).
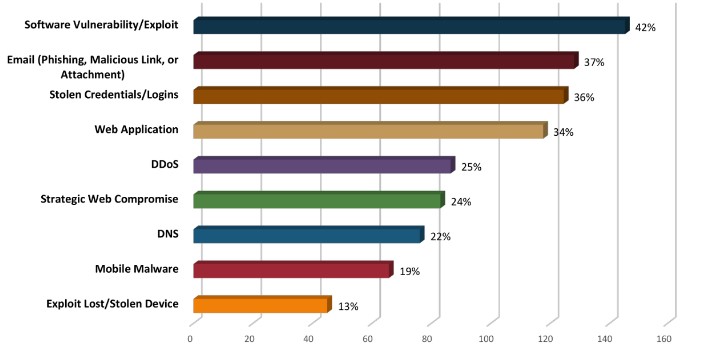
- Email fraud was the 2nd most frequent successful external intrusion method in 2017.
- 0.5% of the top million domains are protected from impersonation by email authentication.
- Implementing email authentication would save the average company $ 8.1 million per year in cybercrime costs—$ 16.2 billion annually across the Fortune 2000.
- Business Email Compromise (BEC), also known as CEO impersonation, losses are up 1,300%
Reducing your Business’ Risk of Email Fraud
Most email security experts agree that implementing two encryption and authentication standards are the first steps to reducing the number of cyber security gaps that have been proven to increase risk of email fraud.
- DMARC: The first standard, Domain-based Message Authentication, Reporting, and Conformance, or DMARC, authenticates an email domain, ensuring that the sender’s information aligns with the known information about the authenticated domain. DMARC has been found to detect the majority of email spoofing and impersonation and handle them according to the receiver’s procedure – usually by flagging them as spam.
- STARTTLS: The second standard, called STARTTLS, is a command that orders a secured connection that subsequently encrypts the email data being sent and received.
DMARC and STARTTLS standards have proved so effective at email fraud prevention that, on October 16, 2017, the U.S. Department of Homeland Security ordered ALL federal agencies to implement both of them within 90 days.
Federally Mandated Email Regulations for Businesses
DHS isn’t the only organization requiring email encryption as part of their technology regulations and compliances.
- HIPAA: Those entities in the healthcare industry that are required to be in compliance with the Health Insurance Portability and Accountability Act (HIPAA) must implement access controls, audit controls, integrity controls, ID authentication, and transmission security before an email correspondence that includes personal health information is considered to be “in compliance”.
- PCI-DSS: Companies that use customer credit card information are required to meet PCI data security standard. The PCI-DSS expressly advises organizations to never use email, encrypted or otherwise, to share credit card data. Because emails are generally stored for long periods of time, it violates the PCI rules regarding card information storage after authorization and maintenance of access control at all times. Still, many PCI compliant businesses choose to use email encryption as an additional security measure.
Catalyst Technology Group Has Your Back!
For most small businesses, the idea of tackling any type of email fraud prevention on their own is extremely overwhelming. It’s a world of protocols and acronyms that the average IT decision maker often prefers to avoid altogether – and that’s just encryption. To get the maximum productivity while maintaining network and data security, modern businesses should leverage spam filters, antivirus and malware scanning, archiving/storage, hosting considerations, acceptable use policies, access control, and more. In the end, an email solution can have a large impact on a company’s daily operations.
The good news is that you don’t have to fight cybercriminals alone! Catalyst Technology Group is well acquainted with all types of cybersecurity – including email authentication and encryption. Our experts will help you find the perfect email fraud protection strategy to meet the needs of your business. Contact us at (317) 705-0333 and get encrypted.
Tip of the Week: Looking to Free Up Hard Drive Space? This Free Tool Can Help

No matter how much we wish it weren’t so, all PCs have limited amounts of storage space on them. This means that the user will eventually run out of space, and they will have to find a way to resolve this issue as soon as possible so as to avoid unsaved work. Plus, your performance will take a hit, so it’s best to look for a way to resolve this issue. Thankfully, a free tool like WinDirStat can help you free up space by identifying where all of your free space is being taken up, and how you can make some wiggle room with your PC’s largest files.
Before we dig into the details, we want to add a disclaimer about deleting any large files that might be on your company-provided computer. Users should always check with a company’s IT administrator before deleting anything large like this on their PC. By doing so, you could avoid accidentally deleting files and apps that are crucial to your organization.
The Windows Directory Statistics, or WinDirStat, is a tool that lets you see a visual “treemap” of how the space on your hard drive is being used. To download this free app, just go to the developer’s website: https://windirstat.net/download.html
When you first open up WinDirStat, the program will read your drive’s directory tree and show you three displays:
- Directory List: You’ll see what looks like a tree view of Windows Explorer, but it will be sorted by file type and subtree size.
- Treemap: You’ll be shown the entirety of the directory tree.
- Extension List: This shows statistics regarding file types.
Each of these files are represented by colored rectangles, and the size is proportionate to the file’s size. You will notice that these rectangles are arranged by directories and subdirectories. Therefore, the rectangles will be proportionate to the size of the subtrees. Additionally, the colors of the rectangles will indicate file type, and you can use the extension list to find the color that you’re looking for.
With this knowledge in mind, you’ll be able to make the best decisions possible regarding which files you want to delete to free up space for other uses However, you still need to be wary that deleting this files isn’t the only option at your disposal. Deleting large files that could hold value, like a video, simply because you don’t access it frequently, would be foolish. It’s ideal to simply get it removed from your drive through the use of an external drive, a network drive, or the cloud.
Granted, if your goal is to free up hard drive space and improve the way that your PC functions, you’re better off reaching out to professional technicians like those at Catalyst Technology Group. We can help your organization get the most out of its technology solutions, including your data storage procedures, reach out to us at (317) 705-0333.
Looking to Boost Productivity and Capital? Outsourced IT Can Help

There are a lot of moving parts in a business, but overall the goals are simple. If you make more money than you spend in operational costs, you’re considered a success story. However, it’s not always easy to achieve this balance–especially when you’re a small business with a limited workforce and budget. How can you cut costs and increase your bottom line?
One of the biggest things holding back smaller organizations is the need to invest large sums into expensive operational necessities, which inevitably leads to less flexibility in the face of critical business decisions. If your budget is stretched to the maximum, you won’t have the funds required to respond to an emergency situation, like a hardware failure or other similar catastrophe. This is a tricky situation to get out of, and it might require some creative cuts to your budget in order to just get by. This isn’t how you want to manage something as critical as your business’s budget.
Modern businesses rely on technology solutions in order to maintain acceptable levels of productivity and efficiency, and we at Catalyst Technology Group want to help your business achieve greater heights by offering managed IT services. SMBs have to invest a lot of time and resources into their technology infrastructure, but we can make it more affordable through proactive maintenance and management, providing more time for your organization to stay productive and efficient.
How Managed IT Works
Catalyst Technology Group’s managed IT services work by providing your organization with a single point of contact for all of your technology needs. This includes knowledgeable consultants and trained technicians that can help you make informed decisions regarding your IT infrastructure. Here are some of the core services that we offer:
- Network monitoring: Thanks to our expertise and a certain level of automation, Catalyst Technology Group can keep close watch on your network to prevent issues from evolving into downtime-causing problems.
- Backup and disaster recovery: Too many businesses believe that their data isn’t important enough to warrant a backup solution. Keep in mind that the success of your organization is heavily dependent on your ability to access information that you’ve gathered over the years, including internal records and client information. You need to safeguard these important assets so that they can survive even the most devastating disasters, like a fire, flood, or even a cyberattack.
- Cloud-based services: One of the biggest capital expenses organizations have to deal with comes from upgrading their computing infrastructure. By this, we mean all of the critical business applications that you use on a daily basis. Cloud-hosted versions of these software solutions are always up-to-date, and they are generally cheaper per user on a subscription basis compared to the expenses of software licensing. All-in-all, cloud computing can be used to cut costs in regard to email hosting, data storage, and even virtualization, allowing you to improve operations while eliminating unnecessary costs.
Long story short, managed IT is capable of removing unnecessary costs from your budget, while improving operational efficiency, allowing you to better spend your assets elsewhere. With Catalyst Technology Group on your side, you’ll be able to properly leverage new and innovative solutions to save money and get the leg up on your competition. To learn more about managed IT services, reach out to us at (317) 705-0333.

