Email Malware is the New Schrӧdinger’s Cat
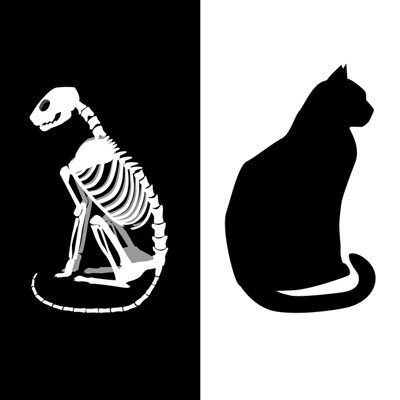
There is a famous thought experiment devised by physicist Erwin Schrӧdinger, describing a very particular paradox in quantum physics through the experience of a cat. While Schrӧdinger’s cat was initially intended to demonstrate a very different phenomenon, it can also be applied to something that all businesses need to consider: their email security.
Schrӧdinger devised the thought experiment to combat the Copenhagen interpretation of quantum mechanics, which posited that, when unobserved, an object can exist in all states, and reverts to one if observed. In Schrӧdinger’s thought experiment, a cat was hypothetically shut in a box with a small enough amount of radioactive material to only have a 50/50 chance of being detected by a Geiger counter. If it was, a hammer would break open a container of poison, killing the cat. The premise was that, if the Copenhagen interpretation was correct, the cat could be assumed to be both alive and dead simultaneously until it was observed to be one or the other.
While Schrӧdinger’s cat was meant to discredit the Copenhagen interpretation, there is a modern version of this thought experiment that businesses should be concerned about. This version focuses on email, and the attachments that often come with it.
It is no secret that email is a very popular way for cybercriminals and other online mischief-makers to deliver their tools. If we treat emails the way that Schrodinger’s cat was approached, any email could feasibly contain a malicious threat, as well as no threats at all. The thing is, while determining if Schrӧdinger’s cat was alive or dead would be a relatively harmless activity (except potentially for the cat), finding out whether or not an email attachment is infected could cause quite a bit of damage to your system.
Fortunately, there are ways to protect yourself and your system against threats like email malware and phishing attempts. Antivirus and anti-malware scanners can catch many threats on their way in, and a spam blocker can help keep out many more.
If you’d rather know for sure that your inbox doesn’t contain any threats (or dead cats), let Catalyst Technology Group suggest a few solutions. Give us a call at (317) 705-0333.
Is Your Mobile Device Safe from Malware?

Mobile devices are becoming more important in business use, which means that their security needs to be a serious consideration. While for most of its history, the telephone’s function was limited to sending sound, the new functions that these new mobile devices have give them more utility, but also make them more of a target for threats, including viruses.
Protecting a mobile device against viruses will require the installation of a mobile antivirus solution. This is despite the presence of Play Protect, an internal safeguard that Google has developed to stop malicious applications and updates. Play Protect scans everything in the Play Store, both when it is first added and whenever it is installed on a device, as it works to protect against malware and other threats that target mobile devices. Unfortunately, as security goes, Play Protect isn’t very effective.
On average, real-time malware detection rates hover at 94.8 percent. After four weeks, these rates rise to 96.9 percent. Play Protect’s rates are at 48.5 percent real-time and 66.3 percent after four weeks.
Installing an additional antivirus application can better protect your device. Even better, many of the applications with an above-average detection rate are available for free. By delivering the services of a comprehensive mobile security suite, many of these solutions are very similar to Google Play Protect’s intended purpose. However, some of these apps do have some downsides.
Some antivirus applications, for example Avast Mobile Security and McAfee Mobile Security, rely on ads for support. This may turn some users off. Norton Security Antivirus allows remote locking capabilities, but doesn’t block malicious websites.
Modern business requires a mobile device management strategy that keeps you secure against threats and issues of all kinds. Catalyst Technology Group can help you to identify and implement the security solutions you need, including the ones for your mobile devices. Call (317) 705-0333 for more information.
100 Countries Hit By Android DDoS Malware

In what is one of the first attacks of its kind, a botnet dubbed WireX swept across 100 countries, controlling over 120,000 IP addresses at its peak. The factor that made WireX so unique was the fact that the botnet was made up of Android-powered devices that had one of 300 malicious apps downloaded from the Google Play Store.
How It Works
WireX was designed to use HTTP requests to bombard their targets, directing as many as 20,000 requests to a target every second to use up the target’s server resources. This number of requests may not have been effective, if it weren’t for where WireX would direct its attack on the victim site. Rather than just sending 20,000 requests every second to the website as a whole, WireX would target specific pages that used more of the site’s resources. Search pages were frequently targeted for this reason.
Why Is WireX So Nasty?
There are a few factors that contribute to why WireX managed to cause such a big fuss, so quickly.
First off, although WireX is an Android-powered mobile botnet, the traffic it sends to the targeted website appears to be regular mobile browser traffic. This is a problem, because most experts who focus on defending companies from DDoS attacks utilize filters that help them to sort the malicious traffic out from the legitimate traffic. This is more difficult with WireX, as it includes its own fully-functioning browser that hides its information from the targeted system.
In addition to this, WireX also leverages SSL as a part of its attacks, which usually protects an Android user’s browser session. In this case, however, it only makes WireX more difficult to detect.
Defeating the DDoS
It ultimately took a team of experts from Cloudflare, Akamai, Flashpoint, Dyn, Google, Team Cymru and EiskIQ to stop WireX. The seven companies needed to pool their resources and data on WireX in order to identify it as a mobile-based attack, and then to identify the 300 malicious Google Play Store apps that delivered it. While these apps have not been named to the public, they were often media players, ringtones, or storage managers. Google has since blocked these apps from the Play Store, and has also removed them from the devices that were infected.
So, What Can You Do?
Your most effective defense against threats like WireX and other applications that sneak in malware is to simply not download applications that you don’t trust, as well as to educate employees on why they shouldn’t either. For more information on the latest threats and how you can protect yourself, call Catalyst Technology Group at (317) 705-0333.

