3 Reasons That Remote Monitoring and Management Is A Good Choice

The businesses of today rely on technology in order to function, which means that their technology needs to be in top shape. However, this requires a sizable time commitment, something that most businesses will have trouble seeing through. Help comes for these businesses in the form of remote monitoring and management.
What Does RMM Do?
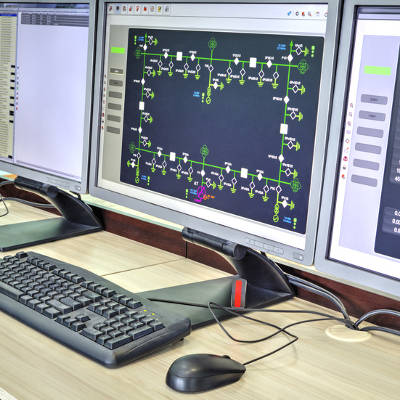
Remote monitoring and management is just about what it sounds like–a business has their IT monitored for issues, which means that these issues can be spotted and dealt with before they have an adverse effect on that business’ systems. Since this process is completed remotely, there’s no need for the managed service provider (or MSP) to send a technician for an on-site visit.
Improved Insights
One of the most useful results of RMM is the high quality of insights and data you are able to collect, including which threats are most commonly detected by your solution. This data allows the MSP to ensure that you are prepared to deal with these threats, potentially thwarting an event that could have caused serious downtime… or worse.
Preparation
In addition to working to keep threats away from your network, an RMM also helps to ensure you are ready for when an issue does slip past. Through data collection, you will be alerted and a ticket created whenever an issue is detected in your systems and your MSP will get to work to resolve it. If your MSP’s IT professional can, they will mitigate the problem and maintain your productivity–or at the very least, begin to identify and resolve the issue at hand.
Predictable Pricing
As one part of a managed service offering, RMM comes with the benefit of a fixed price. We rely on your trust to deliver our services, and we find that a single, honest price helps to foster that trust.
This has just been a brief sample of how RMM can bring your business benefits. To find out more about RMM and how it can help your business, give us a call at (317) 705-0333.
Project Management: What You Need to Know

Every business has IT projects they want to complete. Whether it is a small change like introducing a public cloud platform, or a large one like migrating all your data from four servers onto one, you have to expect situations will arise that will make you want to pull your hair out. To overcome the challenges that come with any major IT project, consider these four points.
Understand What You Need
By understanding exactly what your company stands to gain from any new IT project, and being able to properly strategize to meet those ends, you can really help mitigate the rate of failure of said project. Some questions you should ask before getting started include:
- What is the best result from undertaking the project?
- What are the project’s potential benefits?
- Will this project affect the ability for multiple departments to continue operations as normal?
- Will the project affect your relationships with clients/prospects?
- How much, if any, downtime will the project cause?
- Does your staff need to be informed about the status of the project?
Planning for Delays
There are a litany of potential issues that can cause delays to a project. Typically, during the duration of a project something that wasn’t in the game plan will happen and will set the implementation timeline back. To guarantee that your project isn’t going to cause headaches for more people than it has to, anticipating that there will be a hiccup or two along the way is a solid practice. Providing your implementation team some time to iron out the kinks can go a long way toward having a solution that is implemented properly and ready to be utilized. And, if for some reason no problems arise, you will actually come in under budget, which is great for every business.
Measuring Progress and Hitting Benchmarks
If you are taking on a large IT project, gauging the success of it can sometimes be difficult. By breaking up the project and setting up very clear benchmarks, the overall implementation will benefit. Since there are a lot of facets to every IT project, including budget, timeline, and the unforeseen inefficiencies that we talked about above, setting up a system to best understand where you are with a project is a must. The use of key performance indicators (KPIs) can substantially improve your overall understanding of the project. Catalyst Technology Group uses some of the following metrics when performing our IT projects:
- Actual cost
- Cost Variance
- Earned Value
- Planned Value
- Return on Investment
Communication
Of the four points in this blog, this is the one that is most neglected. Typically, it is the job of the project manager to, well, manage the project. To that end some managers don’t find it necessary for their resources to know the full scale of the project as they are traditionally only performing specific tasks. In our experience, to best drive a project home, and to get the best work out of your technicians, it is important that they are emotionally engaged with the success (or failure) of the entire project. Moreover, if the project has an effect on multiple facets of your business, communication is essential to ensure you aren’t hit with profit-killing downtime in moments when it is not completely expected.
There are many pieces of software currently on the market to help project managers run efficient projects. They have integrated options to ensure that communication is maintained and benchmarks are hit. These programs can make sure your team is keeping forward momentum, as it is essential to a project’s success.
Like most situations, an IT project will have unforeseen issues. To keep these issues from become problems that can cost your organization dearly, consider reaching out to the IT professionals at Catalyst Technology Group. Our technicians understand just how much technology means to the modern business and can help consult you on how to get what you need done right. To learn more, call us today at (317) 705-0333.
Project Management Tips From the Pros

If you’ve ever managed a major IT project, you’re probably well acquainted with Murphy’s Law: “Anything that can go wrong, will go wrong.” Every project is going to have some rough patches. The key to overcoming these challenges lays not with the execution of the plan, but with the preparation. Here are four things to consider when you’re planning out your next long-term IT project.
Know Your Needs
Believe it or not, understanding exactly what your company needs from a project and translating that into a well-defined strategy with realistic goals may be the difference between a success and failure. First, it’s best to look at the big picture.
- What is the desired result?
- What does the project do for your business?
- How will the implementation of this project affect other departments?
- Will the project directly impact clients/prospects?
- Will there be any downtime?
- Does the team need to be educated about this project?
Budgeting for the Unknown
Prices go up. Projects get delayed. Accidents happen. More often than not, you’re going to run into an unplanned incident during the duration of your project. The best way to make sure that your budget doesn’t come up short is by anticipating that there will be unforeseen expenses. Whenever possible, it’s preferred that you give yourself a bit of ‘wiggle room’ within your budget. Of course, you can’t predict the future – but you can look to previous projects for an idea of what sort of snafus you are likely to encounter. Giving yourself a bit of cushion when planning out your budget might end up saving you big time down the road. And if it turns out that you didn’t need that extra money, then congratulations! Your project was completed under budget!
Determine Benchmarks and Measurements
Especially important during long term IT projects is figuring out ways to measure and gauge the project’s progress. You will want to determine a plan for these measurements before you begin the project. This will help you maintain forward momentum, keep your budget in check and show areas that need improvements for the next time you have a similar project. Key performance indicators (KPIs) are ways to measure that success. Keeping track of the following metrics will help you get a grasp on the way your project’s progress throughout the execution:
- Actual cost
- Cost Variance
- Earned Value
- Planned Value
- Return on Investment
Too often in a project’s execution, only the project managers will know how the project is fairing. Everyone else is only privy to the sections of the project that apply directly to them. Project managers are there to drive the project – and part of that is communicating with resources – both inside and outside of the project. For example, if your project is going to require your network to be offline, giving advance warning to those who will impacted by this downtime is not only courteous, but keeps your project on track. There is nothing like having to delay your progress because there was an important meeting scheduled for the time you had planned on bringing the network offline.
There are many programs and applications available to those who are looking for ways to improve organization and communication throughout your project. Project management software gives PMs a unified solution where they’re able to track inventory, budget, KPIs, resources and a whole host of parts of a project in motion.
As with most things in life, projects rarely go as planned. The only thing that a project management team can do is make an effort to plan ahead, anticipate needs, and be ready to face whatever challenges are thrown their way. Do you have an IT project in mind but are unsure of how to manage and execute it? Contact Catalyst Technology Group today at (317) 705-0333.
Unified Threat Management Keeps Your Network Safer

Network security is equally important for businesses of all sizes. Ensuring that your infrastructure remains firm is one of the most crucial tasks in managing a business. You don’t have to do it alone, though. There are enterprise-level tools available that can give small businesses the same security standards as larger organizations, and it all starts with a Unified Threat Management (UTM) solution.
A UTM takes four of the best enterprise-level tools and combines them into one great package. You’ll have a firewall, antivirus, spam blocker, and content filter in place to keep your business secure. You’ll quickly discover that this is the best way to handle network security.
Firewall
Your firewall is the first line of defense for your network, tracking any incoming or outgoing data to keep threats at bay. If you keep threats from entering your network in the first place, you’ll decrease the likelihood of your business suffering a data breach or other similar attack. Granted, even the best firewall can’t keep out all threats, which is why the rest of the UTM is particularly important.
Antivirus
You might notice that most desktops come with a consumer-grade free antivirus, but this isn’t ideal for business purposes. It will only provide a minimal defense at best. Meanwhile, an enterprise-level antivirus solution can scan your system to check for any known threats on your network, including viruses, malware, spyware, and so much more. This type of tool is often the only way to find some of the more scrupulous threats on your network, so it’s a critical tool for any business that wants to take network security seriously.
Spam Blocking
Spam can be both a waste of time and a threat to your organization’s security. A single employee downloading the wrong attachment or visiting a malicious website could become a major problem for your business. Data could be compromised in the fallout, which could damage your organization’s reputation and subject it to compliance fines. The most effective way to protect yourself from spam is a proactive solution that keeps suspicious messages out of your inbox in the first place. You can’t click on messages that aren’t there, right?
Content Filter
The Internet contains practically endless threats, and if you’re not careful, they can find their way onto your infrastructure via your employees’ browsing practices. There is malicious content on the web that can install malware or infect your computer with viruses. Furthermore, some websites might try to farm credentials from your employees, including personal or sensitive information. A web content filter can block these websites from being accessed on your network, allowing you to keep employees from accessing unsafe or wasteful online content. Plus, it can be implemented on a per-user basis.
Is your organization’s network lacking proper security measures? If so, Catalyst Technology Group can help. To learn more, reach out to us at (317) 705-0333.
Remote Management and Monitoring is Ideal for SMBs
When you experience troubles with your technology, you don’t have time to just sit around and wait for the problem to resolve itself. You need someone by your side to assist with the problem. Yet, many small businesses don’t have the luxury of an in-house IT department that can help its employees resolve problems quickly and efficiently. How can you avoid this common issue and keep downtime to a minimum in the process?
The clear solution to this issue is working with an outsourced IT provider that offers a remote management and monitoring solution. By remote management and maintenance, or RMM for short, we are talking about the ability to remotely access your systems and resolve problems in real time without sending a technician on site. This is a great solution that allows your organization the opportunity to completely cut out the waiting period, and instead get the problem resolved so that your employees can get back to work.
We’ll discuss some of the great ways that your organization can benefit from remote monitoring and management.
You Don’t Have to Wait for Help
Most issues that your team will encounter with its business technology can be solved without an on-site visit. This means that you get your support in a more efficient and less time-consuming manner, allowing you to get right back to work without experiencing crippling downtime. All the technician needs to do is remote into your computer and address the problem in that way. Of course, not all problems can be resolved without an on-site visit, so some more hands-on tasks will still require the journey to your office. Yet, you’ll be able to rest assured that your organization won’t have to put up with an unnecessary waiting time for assistance.
Your Systems Are Maintained Properly
If you don’t have an internal IT department to keep watch over your systems, an outsourced IT provider can provide this valuable service with our RMM tools. We can monitor your systems for any concerning activity, including unexpected hardware failures or the telltale signs of problematic occurrences. By preventing issues from evolving into major problems, you can take preventative measures in a timely manner and limit the damage done by downtime. Plus, we can administer patches and security updates remotely as well, all so you can stay focused on what matters most–running your business.
Your Budget Will Thank You
Why hire an entire internal IT department if you don’t need to? By outsourcing to an IT provider, you pay only a monthly fee for any services rendered, rather than an entire salary for the services of an in-house technician. You can then invest the funds saved into various other more profitable endeavors, eliminating any unnecessary costs within your organization.
Does a remote monitoring and management service sound like a perfect fit for your business model? If so, reach out to us at (317) 705-0333. We’ll work with you to ensure that you get the amount of service you need.
Tip of the Week: How To Be Better At Time Management

It would be hard to find someone who has never experienced the feeling of a time crunch, a situation where someone has more to do than they had hours to do it in. This feeling can be reduced by enhancing productivity through better time management. For our tip this week, let’s discuss some methods to improve time management within your office.
Simplify and Streamline
Before you devote your time to completing a particular task, it helps to determine whether or not that task needs to be completed now or if it can wait until later. Focusing on what needs to be done sooner allows you to better plan to fulfill these responsibilities.
In this way, it helps to follow whatever schedule you have in place, committing your full attention to accomplishing what is outlined for you to do. By eliminating distractions around you and focusing on the task at hand, you will be able to complete your duties more quickly and with greater accuracy.
Furthermore, is the current process to complete a given task as efficiently as possible, or are there redundancies and other unnecessary elements involved? Eliminating these elements will only allow you to cut out extra time that could be better spent elsewhere.
Planning for Success
Of course, the key to time management is establishing how much time you have to manage. It helps to put together a schedule to follow that firmly sets important events, such as project deadlines or meetings. This will tell you how much time you have to devote to your other tasks. Once this time has been established, turn a critical gaze toward the rest of your schedule.
Establish which of your remaining tasks need to take priority over the others, and incorporate them into your schedule accordingly. It is also important that you take your coworkers’ schedules into account. If they need you to complete some task before they can carry on with their work, plan to complete that task sooner, rather than later.
Creating a schedule for yourself to follow throughout the workweek is a solid way to not only ensure that your tasks are attended to, but that you can accomplish them at your peak. For instance, if you know you have a meeting on a Thursday and a deadline to meet on Friday, you can ensure that you give yourself ample time in the beginning of the week to prepare for both. You also need to be sure that your high-priority tasks are given a high enough priority to ensure that they are finished on time.
Preventing Resources From Causing Issues
Communication can be a double-edged sword in any office environment. While it is a necessary tool to remain productive, it can quickly cause harm if misused. For example, cell phones. While they are an excellent tool for communicating, they can only serve a limited use in the professional environment–even as a component of a Bring Your Own Device productivity strategy–and can therefore become a distraction above anything else, wasting precious time.
Yet not every issue with your company’s time management are caused by a human habit. Oftentimes, mismanaged IT can lead to serious issues that will prevent the company’s employees from properly doing their jobs and thereby from being productive.
All’s not lost, however, as Catalyst Technology Group can provide the tools to ensure that your IT is in top shape, freeing you to focus on spending time on improving the other components of your business. Give us a call at (317) 705-0333 for more information.
Does Your Network Management Seem Unmanageable?

There’s no denying that there is a lot to do in a business environment, and some things take longer than others…or at least they should. Is your business investing enough time into its network management, and all the tasks, processes, and responsibilities that it involves?
Your network is key to your success, as it directly influences the capabilities of your end users. After all, if there is a network issue, some or all of your employees will have a reduced capacity to perform their duties–if they are able to at all. This is only exacerbated by the amount of applications that are migrated to the cloud; applications that are critical to the business’ function. If the network fails, these cloud-based applications can’t be utilized, and productivity grinds to a halt.
Fortunately, this can all be mitigated through proper network management and maintenance. Proper network management can assist a business by helping to improve its internal performance and reliability, as well as helping to keep external threats to the network’s security at bay.
As a few examples of the management and maintenance your network is going to need, please refer to the following list.
- Updates, including those to your operating system, drivers, and your software.
- Patches to your cybersecurity systems to ensure that they are updated and resilient.
- Managing and maintaining antivirus across the whole network.
- Predicting and avoiding hard drive failures.
- Maintaining and testing backup solutions to ensure that data will be preserved.
However, there are still other things to be done as well–after all, your business still needs to be run, and those concerns cover far more than just how well your network is managed. Yet at the same time, with an improperly managed network, there could soon be no business for the network to support.
For instance, if your network fails for an extended period, you will find yourself dealing with downtime. This can be due to an improperly maintained piece of network equipment failing, or from someone in your organization improperly utilizing or configuring a part of the network. Either way, without the network being managed and documented, issues like these are likely to be a common occurrence for your business.
If you find that taking care of business has kept you from properly taking care of the business, there’s a solution for you: entrust the management of your network to the pros at Catalyst Technology Group. We can monitor your network remotely and keep an eye on it to make sure there aren’t any internal threats to your business, and that you aren’t unknowingly sacrificing productivity due to an unknown network issue.
We help ensure that a business’ network is in tip-top shape so that business has the ability to thrive. We could do the same for your business as well. Just give us a call at (317) 705-0333 to get started.
Keep Your Best Employee From Becoming Your Worst Problem With Data Management

Chances are that you, like most business owners, have assembled your staff very carefully, looking for people who are the best-in-class, willing to work their hardest for the good of the company. However, this staff will be made up of humans, and will therefore make mistakes. As such, you need to make sure that your data is managed in a way that keeps it safe.
Are you confident that you know where your company’s data is currently stored?
Unfortunately, if you are relying on your eager, diligent staff to allow you to answer “yes” to that question, then you may be answering incorrectly for the right reasons.
The thing about diligent employees is that, well, they’re diligent. They want to get the task at hand done to the best of their ability and as quickly as possible–and if that means they have to work from home, then that’s what they’re going to want to do. Which wouldn’t be a problem, if their home networks were nearly as secure as the ones you have in place at your business.
What’s to be done? You don’t want to discourage your more diligent employees, but you also want to make sure your data is safe.
The easy answer is to meet employees like these halfway. Give them access to a Virtual Private Network to help maximize their security as they access your data remotely. Ask them to have their personal devices checked by IT before they use them to access the network. Ask them if they’re willing to allow IT to remotely wipe their personal device if it should be lost or compromised as a precaution, if they were to be able to use it for work. An established Bring Your Own Device policy will make enforcing this requirement a little easier.
Of course, this does not mean that you should give all employees carte blanche access to all of your data. Network access control solutions are an effective way to restrict your employees from accessing data that is above their pay grade, either intentionally or by accident. Requiring authentication has become the norm in most of society, and so your loyal employees are unlikely to have a problem with it in the workplace. Passwords, PIN access, and other identification factors will prove useful in keeping employees where they are supposed to be, and able to access what they need for their job requirements.
The reason that it is so important to allow your employees to work as they wish is because it will allow them to be productive, without resorting to their own methods outside of company control, which are far less secure than what you have implemented.
For help implementing these features into your IT infrastructure, make sure you give Catalyst Technology Group a call. We have the solutions you need to safely allow your enthusiastic employees to work the way they work best. Give us a call at (317) 705-0333 today.
4 Ways a Unified Threat Management Solution Covers Your Company’s Security Needs

Your company’s network contains a gold mine of sensitive information that you need to protect at all costs. While it’s absolutely the case that you need to make network security a top priority for your business, thankfully, multiple aspects of your security can be covered easily enough by implementing a single, enterprise-level security solution.
The solution we’re referring to is a Unified Threat Management (UTM) tool. It’s a powerful tool that combines the fundamental security features that every business needs, into one easy-to-manage package. If you’re looking to get a handle on your company’s network security, then consider these four ways that a UTM provides comprehensive protection.
Firewalls
A firewall is the first line of defense for your company’s network, protecting your business from the onslaught of online threats trying to sneak their way in. One can go so far as to compare a UTM firewall to a sort of virtual bouncer for your network that; assesses the threat level of your network’s traffic, garners if it’s a security risk, and then clears for passage only what’s deemed to be safe.
Antivirus
Every good firewall needs an antivirus solution to compliment it. After all, some forms of malware are sneakily engineered to play on a user’s ignorance so as to bypass the firewall. In such a scenario, antivirus software is there to quickly catch and eliminate threats such as viruses, trojans, spyware, ransomware, and more. Given the destructive nature of many of these threats, you’re going to want a powerful antivirus solution in place that prevents such viruses from spreading across your network and wreaking havoc on your systems. Additionally, while there are many kinds of antivirus solutions on the market, businesses will want to take advantage of a centrally located antivirus solution like what comes with a UTM. This way, updates and scans can be done automatically and in one fell swoop, instead of being left up to each individual user.
Spam Blocker
Having spam in your inbox is totally annoying, and it can also be dangerous. One common way for hackers to spread malware is by attachments found in spam messages. Plus, savvy hackers will employ spam as a phishing tactic to trick users into opening the message and following its instructions which appeal to emotions. Examples include a fake summons to jury duty, a fake package that couldn’t be delivered, a fake resume for a job opening, etc. A quality spam blocker will prevent these messages from hitting employee inboxes in the first place, which greatly reduces the risk of a user being tricked by spam.
Content Filter
Businesses also need a way to protect their networks from the vast amount of online threats that come from visiting dangerous websites. Unfortunately, it’s all too easy for an employee to stumble upon a website that’s designed to harvest credentials or download an attachment designed to infect your network with a virus or even ransomware. With a content filter protecting your network, you’ll be able to block users from accessing suspicious websites in the first place. Additionally, a UTM content filter allows you to block time-wasting websites like social media, YouTube, Netflix, etc., making it a valuable tool that both protects your network and enhances productivity.
In order to be adequately protected, your business needs all four of these security features. A UTM from Catalyst Technology Group conveniently offers your network protection in all of these ways, and more. To equip your network with a UTM security solution that’s customized to fit the needs of your business, call us today at (317) 705-0333.

