Chromebooks Deserve More Credit than You Might Think

It can be easy to dismiss the simple Chromebook as a limited solution, a one-trick pony of technology. However, while this may have once been true of the devices, more recent models are capable of much more than their predecessors. We’ll address a few misconceptions people have about, and against, Chromebooks.
Tip of the Week: Cortana Can Do Even More than You Might Realize
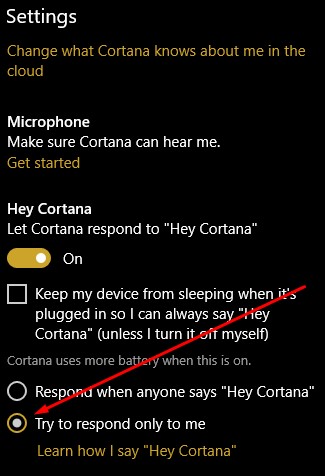
One of the most recognizable names in technology isn’t a person, it’s a virtual assistant: Cortana. While Cortana has been of great use to many users, sometimes that user isn’t actually the person who owns the device and is just someone else in the same room. This can be annoying, but there’s a way to acquaint Cortana with a single user’s voice and listen to them exclusively.
To set this up, you’ll need to access Cortana’s Settings. First, click on the Cortana Icon that appears on the taskbar.

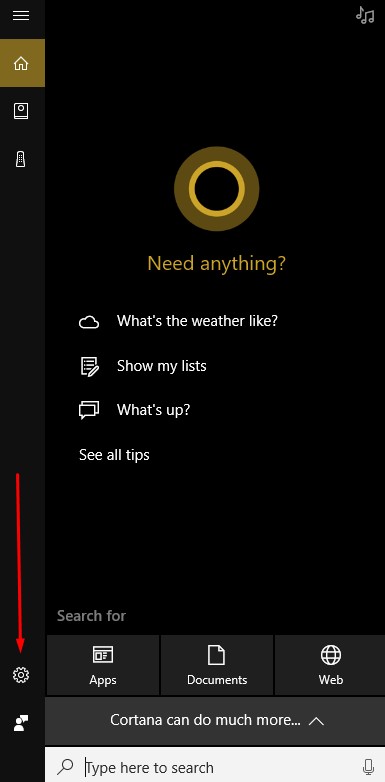
Next, access the settings menu for Cortana by clicking on the gear icon in the Cortana window that appears.
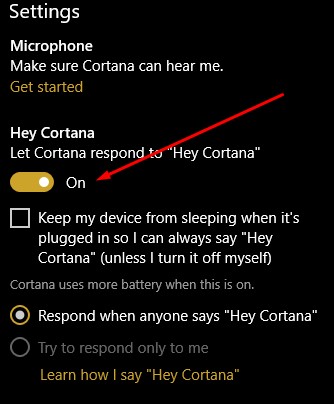
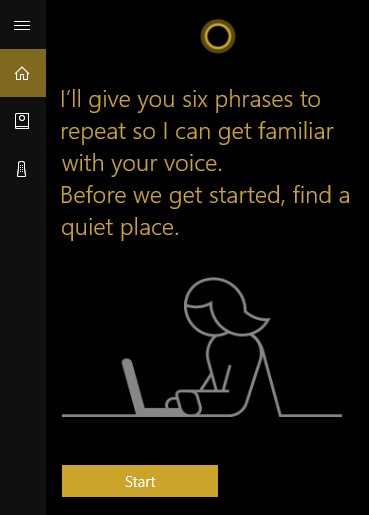
Activate Let Cortana respond to “Hey Cortana” and select Learn how I say “Hey Cortana.”
Once you do so, you will be prompted to recite six phrases so that Cortana can establish how you will say “Hey Cortana.”
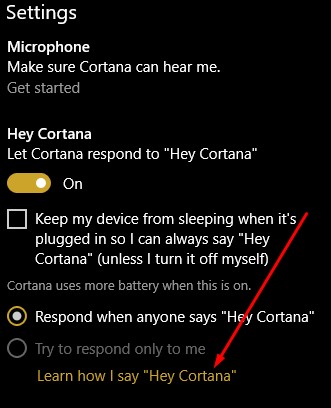
After this exercise is completed, go back to Cortana’s settings and confirm that try to respond only to me is selected.
Cortana is now primed to listen to only you and you can now use it for many purposes, including to navigate Windows 10.
Are there any other assistants you use, like Alexa, the Google Assistant, Siri, or Bixby? Which one is your favorite? Tell us why in the comments section!
Leveraging AI Might Be What Stops Hackers
There are times that hackers can’t interfere with data, and then there are times that hackers really can’t interfere with data. CERN, the Conseil Européen pour la Recherche Nucléaire (European Council for Nuclear Research) maintains far too powerful of a computer grid to risk it falling into the control of hackers. To protect it, CERN leverages the cutting edge of security to protect its European Laboratory for Particle Physics: artificial intelligence.
There are a few reasons that using AI as a part of security is a solid strategy. First, it gives users a fighting chance to stay abreast of the changes that malware makes. As a means of fighting threats, the scientists at the European Laboratory for Particle Physics are teaching their AI to identify, extract, and eliminate threats on the network.
This is saying something, especially considering the resources needed to operate CERN’s famous Large Hadron Collider and Worldwide LHC Computing Grid. The LHC collected around 50 petabytes of data between January and June of 2017–and all of the data it collects is shared to a network of 170 research facilities across the globe. These facilities can even be supported by the vast computing resources within this network as needed.
This setup provides a few challenges for those responsible for maintaining CERN’s cybersecurity. First, maintaining computing power and data storage capabilities, while second, securing their global network against threats.
To accomplish this, CERN has turned to AI and machine learning so their security systems can differentiate between usual network activity and activity from a malicious source. Their AI is still being tested, but that doesn’t mean that there aren’t similar solutions that you can’t leverage to protect your business.
To clarify, we aren’t talking about sentient androids with human qualities and behaviors as one would see in a movie. CERN’s security AI probably isn’t going to find itself feeling unrequited love for a break room toaster. Rather, we’re discussing a tool that is much more accessible than you might initially realize. For instance, Google. Each time you press ‘Enter’ to run a search, the results are compiled, indexed, and categorized without the immediate involvement of a human being. Through machine learning and hundreds of other factors, Google can draw the most relevant results it can for you, specifically.
This allows search results to be delivered faster than the eye can blink, and millions of results to be balanced and compiled just as quickly. Imagine the difference we would see if human beings delivered search results: biases would influence the results, Google would be bankrupted by the staffing costs, and the speed of return would slow to a crawl.
AI’s capabilities are also extremely well-suited for security needs, as it can tirelessly run penetration tests, patch vulnerabilities, and scan for flaws. Improving defenses, like spam blockers and firewalls, can continue at all hours without the human need for a break. With the ability to draw upon and utilize security resources at inhuman speeds, hackers and other malicious actors will have a much harder time.
While true AI is still in the realm of science fiction, we’re getting much closer to making it fact.
What do you think? Is AI the way we will secure a business’ network in the near future? Sound off in the comments section with your thoughts!

